Security Logs,Reimagined.
Next-generation hyperlog compression + signal extraction. Reduce SIEM costs by 50-90% without losing analytical fidelity. Enterprise-grade log optimization for Splunk, Elastic, and cloud platforms.
Security Logs Have BecomeUnmanageable
Enterprise security teams face an impossible tradeoff: pay millions for storage, or lose visibility into threats.
Repetitive Logs
Firewall logs are 70-90% redundant. The same events, repeated endlessly, clogging your pipeline.
Exploding Costs
SIEM vendors charge by the gigabyte. Enterprises hemorrhage millions annually on noise.
Buried Signals
SOC teams drown in data, missing critical threats that hide in plain sight.
Zero Value
Most ingested logs contribute nothing to detection, investigation, or compliance.
The Cost Crisis in Numbers
Enterprises pay SIEM vendors by the GB. LogSlash changes everything.
LogSlash Changes theEconomics of Logging
Transform repetitive logs into structured, compressed, high-signal hyperlogs — reducing ingest size by 50-90% without losing fidelity.
Hyperlog Compression
Merges dozens of redundant events into single, structured hyperlogs with complete semantic preservation.
Time-Window Aggregation
Intelligent windowing captures complete start-to-end event semantics across configurable time boundaries.
Lossless Fidelity
Preserves every critical detail needed for security investigations, threat hunting, and compliance.
Patent-Protected Pipeline
Proprietary transformation methodology backed by issued patents — defensible competitive advantage.
Compression Windows
Choose your compression window based on operational needs — from real-time monitoring to historical archival.
Historical compression reaches 90%+ for archival storage
Universal Coverage Across All Log Types
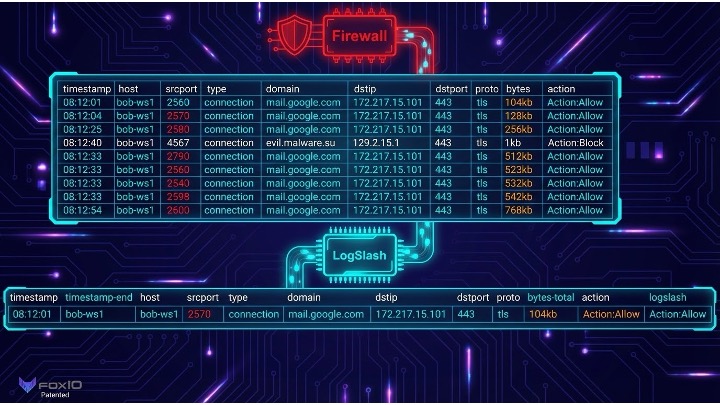
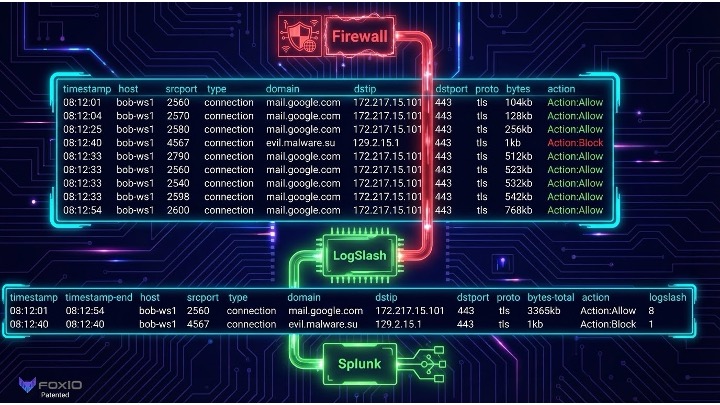
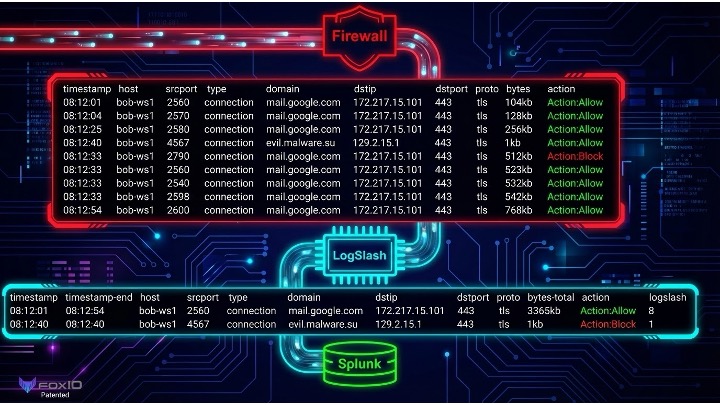
Watch Hyperlog CompressionIn Action
See how LogSlash transforms repetitive firewall logs into compressed, high-fidelity hyperlogs — reducing volume by up to 87.5% while preserving complete analytical value.
Before: Bloated Log Volume
Raw firewall logs — repetitive, expensive, noisy
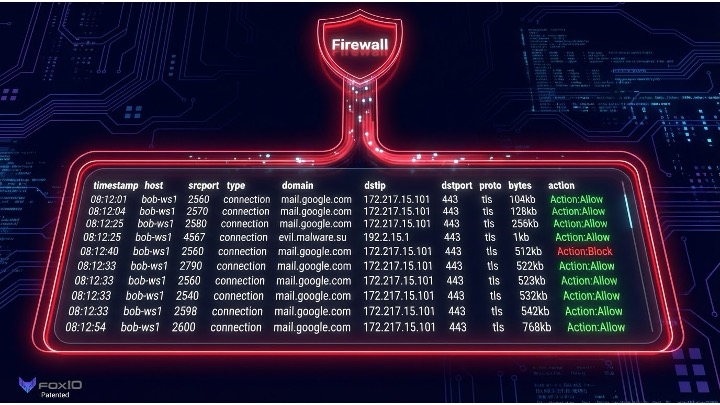
Dozens of repetitive logs → Expensive ingestion → Lost signal in noise
During: LogSlash Transformation
Intelligent compression with semantic preservation
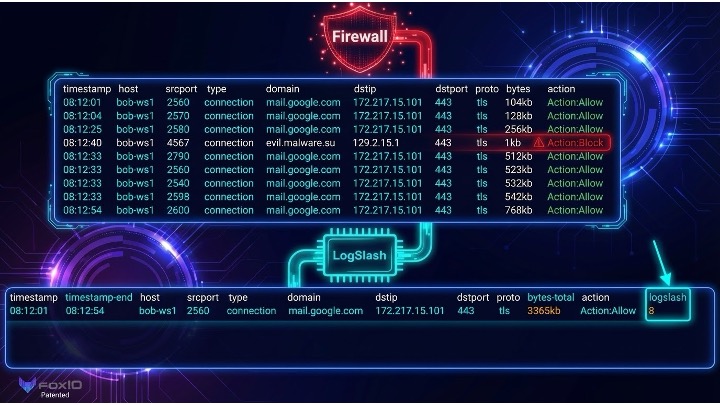
8 raw logs → 1 compressed hyperlog
Unified timestamps + aggregated bytes
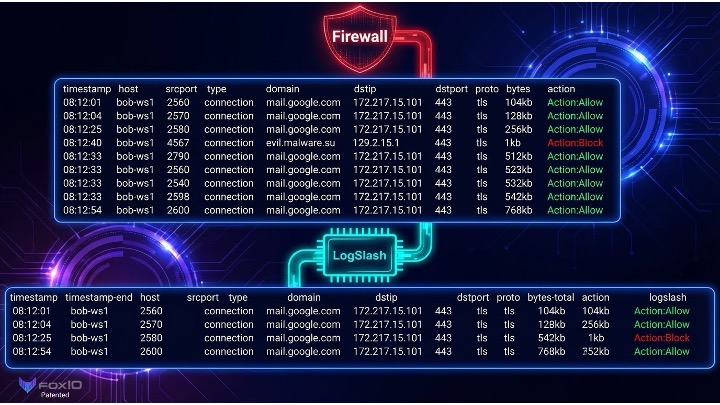
After: High-Fidelity Hyperlogs
Ready for SIEM ingestion at a fraction of the cost
Structured hyperlogs → 50-90% cost savings → Enhanced signal detection
Built by Industry Legends
LogSlash continues the lineage of breakthrough cybersecurity innovation — from the same minds that created the industry-standard fingerprinting protocols used by every Fortune 500 company.
John Althouse
Founder & CEO
Invented JA3, JA3S, and JARM — adopted across the entire Fortune 500 for TLS fingerprinting
Integrated into every major firewall, SIEM, XDR, EDR, and NDR vendor worldwide
JA3/S taught as standard curriculum in major universities worldwide
Co-creator of JA4+, JA4X, JA4S, JA4T — next-gen encrypted traffic fingerprinting standard
Josh Alexander
Co-Founder & CTO
Lead architect of LogSlash hyperlog compression engine and patent-pending algorithms
Deep expertise in enterprise security infrastructure and high-performance systems
Proven track record scaling security products from prototype to enterprise deployment
Core contributor to JA4+ fingerprinting suite and FoxIO security tooling
Strategic Advisors
Michael Barbine
Strategic Advisor
Gary Lipsky
Strategic Advisor
LogSlash continues the breakthrough lineage:
Defensible IP
LogSlash's core technology is protected by issued patents, creating a defensible moat around our compression and signal extraction methodology.
Patent Coverage Includes:
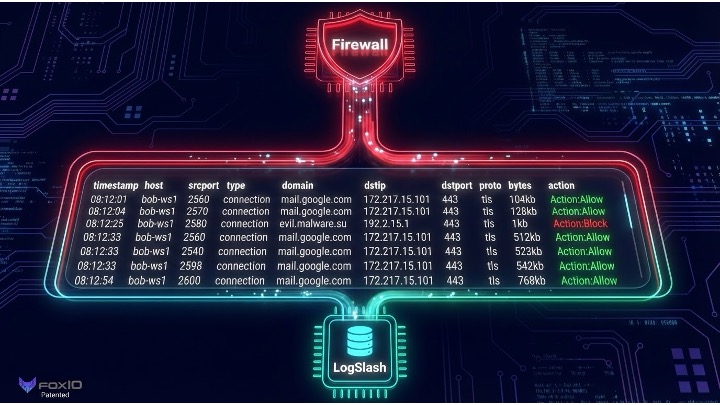
Seamless IntegrationPipeline
LogSlash inserts directly between your firewalls and SIEM, requiring zero infrastructure changes. Drop-in compression that works with every major security platform.
Firewall → LogSlash → SIEM
Raw logs from firewalls pass through the LogSlash compression engine before SIEM ingestion
Multi-Source Aggregation
Compress logs from multiple firewalls and sources before forwarding to your SIEM platform.
Universal SIEM Support
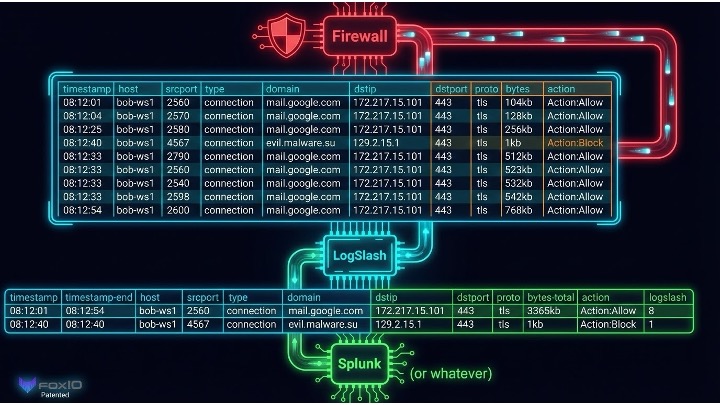
Works with Splunk, Elastic, Chronicle, QRadar, Snowflake — or whatever SIEM you choose.
Complete Data Flow
End-to-end visibility: from raw firewall logs through compression to SIEM analysis
Drop-In Deployment
No changes to existing infrastructure. LogSlash sits between your log producers and consumers.
Universal Compatibility
Works with all major SIEM platforms, cloud storage, and security tools out of the box.
Real-Time Processing
Sub-millisecond compression with zero data loss. Maintain real-time security operations.
Where LogSlashDelivers Value
From SIEM cost reduction to encrypted traffic analytics — LogSlash transforms enterprise security operations.
SIEM Cost Reduction
Reduce Splunk, Elastic, and other SIEM bills by 50-90% without sacrificing visibility.
Cloud Logging Optimization
Compress petabyte-scale cloud logs to hundreds of terabytes.
Encrypted Traffic Analytics
Extract meaningful signals from TLS/encrypted traffic metadata using JA4+.
DFIR Reconstruction
Full-fidelity hyperlogs enable complete incident reconstruction.
Threat Hunting
Structured, deduplicated logs make threat hunting faster and more accurate.
Zero-Trust Telemetry
Support zero-trust architectures with compressed, high-signal logging.
IoT Fleet Telemetry
Handle massive-scale IoT and fleet telemetry ingestion economically.
ML Detection Pipelines
Feed clean, structured hyperlogs into ML detection systems.
Massive TAM
LogSlash inserts directly between producers and storage — capturing value across multiple high-growth markets.
Real-World Savings
Enable Real-Time, Low-Cost,
High-Fidelity Telemetry
for the Global Enterprise
Simple, Value-BasedPricing
Pay based on value delivered. The more you compress, the more you save. No hidden fees.
Platform
Cloud-native SaaS for growing security teams
- Pay only for savings delivered
- Multi-tenant cloud architecture
- Per-enterprise tiering options
- All standard SIEM integrations
- 99.9% uptime SLA
- Email & chat support
Enterprise
Self-hosted for regulated industries
- Annual enterprise license
- Self-hosted or air-gapped deploy
- DoD & FedRAMP aligned
- Custom SIEM integrations
- Dedicated success manager
- 24/7 priority support + SLA
All plans include: Free trial period · No credit card required · Cancel anytime
Ready to Transform YourLogging Economics?
Join enterprises saving millions on SIEM costs while improving detection fidelity. 50-90% reduction, guaranteed.
No credit card required · Free tier available · Enterprise pilots welcome
Learn more about FoxIO